In March 2024, we launched SnortML, an revolutionary machine studying engine for the Snort intrusion prevention (IPS) system. SnortML was developed to sort out the constraints of static signature-based strategies by proactively figuring out exploits as they evolve somewhat than reacting to newly found exploits. After its launch, we’ve continued to take a position on this functionality to assist prospects act on world risk information quick sufficient to cease quickly spreading threats.
Why SnortML?
On the finish of 2020, the checklist of Widespread Vulnerabilities and Exposures (CVEs) stood at 18,375. By 2024, that quantity had skyrocketed to over 40,000. Whereas conventional intrusion prevention programs counting on static signatures are efficient towards identified threats, they typically wrestle to detect new or evolving exploits.
SnortML addresses these challenges with state-of-the-art neural community algorithms whereas guaranteeing full information privateness by working totally on the gadget. The machine-learning engine runs totally on firewall {hardware}, preserving each packet throughout the community perimeter. Selections are computed domestically in actual time, with out the necessity to ship information to the cloud or expose it to third-party analytics. This method satisfies strict data-residency, privateness, and compliance necessities, particularly for vital infrastructure and delicate environments.
That is why our engineers at Cisco Talos developed SnortML. Leveraging deep neural networks educated on in depth datasets, SnortML identifies patterns related to exploit makes an attempt, even these it hasn’t encountered earlier than. Once we launched SnortML, we began with safety for SQL Injection, some of the widespread and impactful assault vectors.
Thrilling New Developments in 2025
What Is Cross-Website Scripting (XSS)?
Cross-Website Scripting (XSS) is a pervasive internet vulnerability that permits attackers to inject malicious client-side scripts into internet pages. These scripts execute within the sufferer’s browser, enabling attackers to compromise person information, hijack periods, or deface web sites, resulting in important safety dangers.
This could happen in two major methods: Saved XSS, the place malicious JavaScript is shipped to a weak internet utility and saved on the server, later delivered and executed when a person accesses content material containing it; or Mirrored XSS, the place an attacker crafts a malicious script, typically in a hyperlink, which when clicked, is “mirrored” by the online utility again to the sufferer’s browser for rapid execution with out being saved on the server.
In each instances, the malicious XSS payload sometimes seems within the HTTP request question or physique. SnortML blocks malicious XSS scripts despatched for storage on a weak server (Saved XSS). It additionally blocks requests from malicious hyperlinks supposed to replicate a script again at a sufferer (Mirrored XSS), stopping the malicious response. By scanning HTTP request queries and our bodies, SnortML successfully addresses all XSS threats.
How SnortML Protects Towards XSS
Let’s dive into an instance as an instance how SnortML stops XSS assaults in real-time. On this case, we’ll use CVE-2024-25327, a not too long ago disclosed Cross-Website Scripting (XSS) vulnerability present in Justice Programs FullCourt Enterprise v.8.2. This explicit CVE permits a distant attacker to execute arbitrary code by injecting malicious scripts via the formatCaseNumber parameter throughout the utility’s Quotation search perform. For our demonstration, no static signature has been created/enabled for this CVE but.
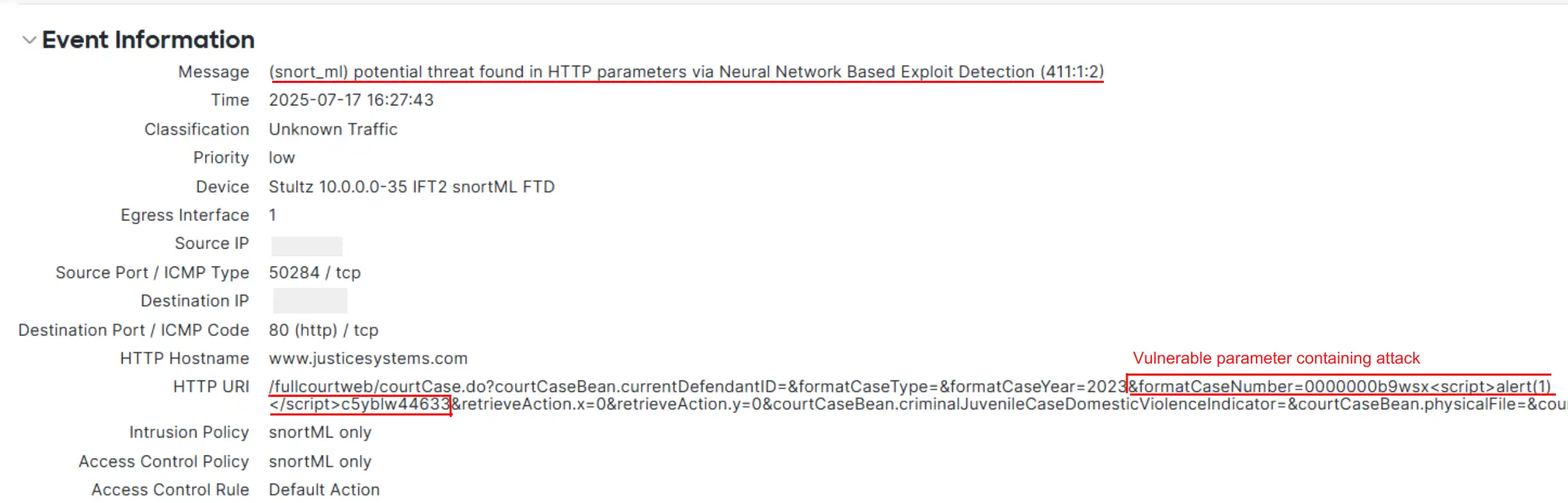
The screenshot beneath, taken from the Cisco Safe Firewall Administration Middle (FMC), clearly illustrates SnortML in motion. It exhibits the malicious enter focusing on the formatCaseNumber parameter. SnortML’s superior machine studying engine instantly recognized the anomalous habits attribute of an XSS exploit, although this particular CVE (CVE-2024-25327) had no static signature. The FMC log confirms that SnortML efficiently detected and blocked the assault in real-time, stopping the malicious script from ever reaching the goal utility.
The Street Forward for SnortML
SnortML is remodeling the panorama of exploit detection and prevention. First with SQL Injection safety, and now with the latest additions of Command Injection and XSS safety, SnortML continues to strengthen its defenses towards in the present day’s most important threats. And that is only the start.
Coming quickly, SnortML will function a quick sample engine and a least not too long ago used (LRU) cache, dramatically rising risk detection pace and effectivity. These enhancements will pave the way in which for even broader exploit detection capabilities.
Keep tuned for extra updates as we proceed to advance SnortML and ship even larger safety improvements.
Able to Discover Additional?
Take a look at the Cisco Talos video explaining how SnortML makes use of machine studying to cease zero-day assaults.
Wish to dive deeper into Cisco firewalls? Join the Cisco Safe Firewall Check Drive, an instructor-led, four-hour hands-on course the place you’ll expertise the Cisco firewall know-how in motion and be taught concerning the newest safety challenges and attacker strategies.
We’d love to listen to what you suppose! Ask a query and keep linked with Cisco Safety on social media.
Cisco Safety Social Media
Share:

